By IP_Address_Match.png: Baccala@freesoft.org derivative work: Zapyon (talk) - IP_Address_Match.png, CC BY-SA 3.0, Link
I've recently read about a couple of boycotts trying to call attention to Amazon's bad labor practices. The most recent of these boycotts hopes to lead a boycott on Amazon's induced buying holiday "Prime Day", in solidarity with striking workers in several fulfillment centers in Spain. I support anyone fighting for a better living!
In my tech-drenched corner of the internet, though, there was some snark observing that it's not enough just to boycott purchasing stuff from amazon.com, because Amazon also silently benefits anytime you use apps or websites that run on their cloud, which is called Amazon Web Services (AWS) and is astonishingly profitable relative to their retail business.
This made me curious: if you wanted to boycott all of Amazon, including its non-retail web services, what's the easiest way to do that?
Counter-intuitively, AWS makes it very easy to do this! They publish and continuously update a list of IP ranges (machine-readable link here), presumably so that people who run various networks can allow internet traffic to/from Amazon to pass-thru.
An IP range, also called a "CIDR block", is a way of specifying a range of IP addresses. Wikipedia has this partially clarifying diagram on the mechanics of a CIDR block:

By IP_Address_Match.png: Baccala@freesoft.org
derivative work: Zapyon (talk) - IP_Address_Match.png, CC BY-SA 3.0, Link
To take a specific example in Amazon's published list of CIDR blocks:
{
"ip_prefix": "18.208.0.0/13",
"region": "us-east-1",
"service": "AMAZON"
},
... 18.208.0.0/13 here indicates that Amazon owns all of the IP addresses between 18.208.0.0 and 18.215.255.255 (covers all IP addresses that match the first 13 bits of 18.208.0.0).
The AMAZON here refers to the specific part of Amazon's universe this range applies to (presumably amazon.com the website in this case) — other values include: AMAZON_CONNECT (Amazon's datacenter internetworking product), CLOUD9 (Amazon's developer software), CLOUDFRONT (Amazon's CDN), CODEBUILD (Amazon's continuous integration product), EC2 (Amazon's server hosting product), ROUTE53 (Amazon's domain name fronting product), ROUTE53_HEALTHCHECKS and S3 (Amazon's kitchen-sink cloud storage product).
Amazon owns all of the IP addresses in these CIDR blocks that are published on that webpage, some of which they reserve for themselves, but others of which are leased onward to other companies that run apps on AWS. To boycott Amazon, you'd need to boycott all of these third party apps running on Amazon's infrastructure as well.
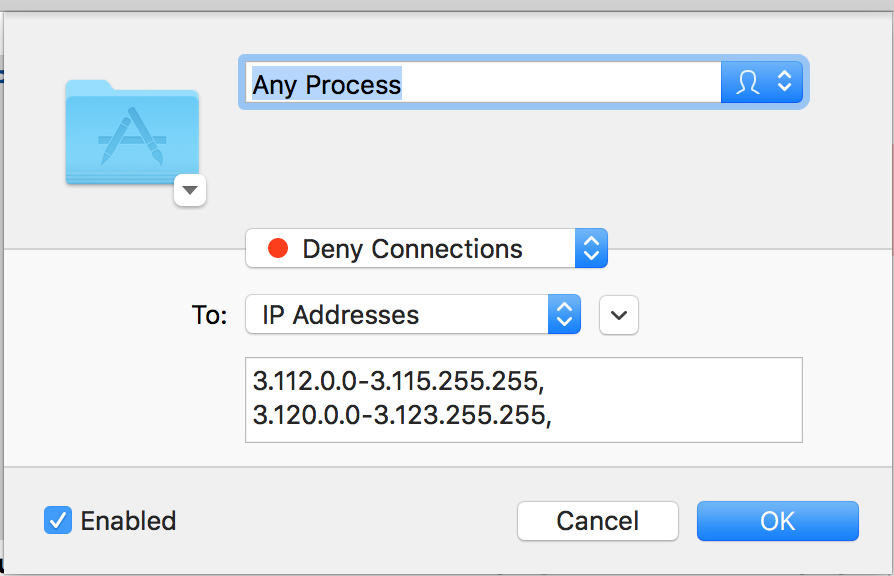
Prerequisites: you'll need jq (an invaluable JSON parsing command line tool), and I'm using Little Snitch on a Mac to block the IP ranges, but probably there are other free and open source tool that would do the trick just as fine.
Step by step:
Run this on the command line:
curl https://ip-ranges.amazonaws.com/ip-ranges.json | jq '.prefixes[].ip_prefix' | paste -sd "," - | sed 's/"//g' | pbcopy
...which will put a comma-delimited lists of CIDR blocks in your clipboard
Open Little Snitch, click the plus button to create a rule, and paste in the contents of the clipboard
...that's it!
Behind the scenes, Little Snitch is intercepting all of the TCP/UDP packets outgoing from your computer (using a Network Kernel Extension) and stopping packets which match an AWS IP from being further processed or transmitted from your computer
Little Snitch also has this frightening/ghoulish way of presenting the filter you've just enabled:
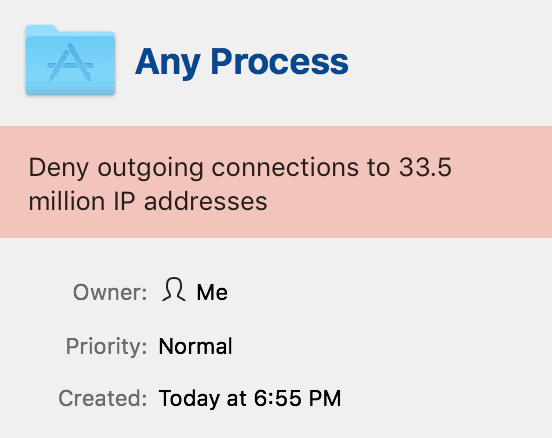
and here's what it looks like when a site that's entirely fronted by Amazon is blocked: